The importance of security should never be underestimated. The consequences of losing data can be disastrous for any organization. For example, the loss of a single unencrypted laptop may have huge repercussions. This could include breaching data protection legislation with the risk of a significant fine, a loss in the confidence of an organization, as well as the risk that sensitive data may fall into the hands of a competitor or third party with malicious intent.
Disk encryption is one method to help minimize the risks by preventing unauthorized access to data storage, to ensure safe information exchanges, safeguard against data leakage, and manage compliance. This form of security is useful for any computer that holds personal information, not only laptops. Disk encryption uses disk encryption software to encrypt the entire hard disk. The onus is therefore not on the user to determine what data should be encrypted, or to remember to manually encrypt files. By encrypting the entire disk, temporary files, which may reveal important confidential data, are also protected. Security is enhanced further when disk encryption is combined with filesystem-level encryption.
Filesystem in Userspace (FUSE) is a software interface for Unix and Unix-like computer operating systems that lets non-privileged users create their own file systems without editing kernel code. This is achieved by running file system code in user space while the FUSE module provides only a “bridge” to the actual kernel interfaces.
Here’s our verdict on the popular encrypted FUSE-based file systems.
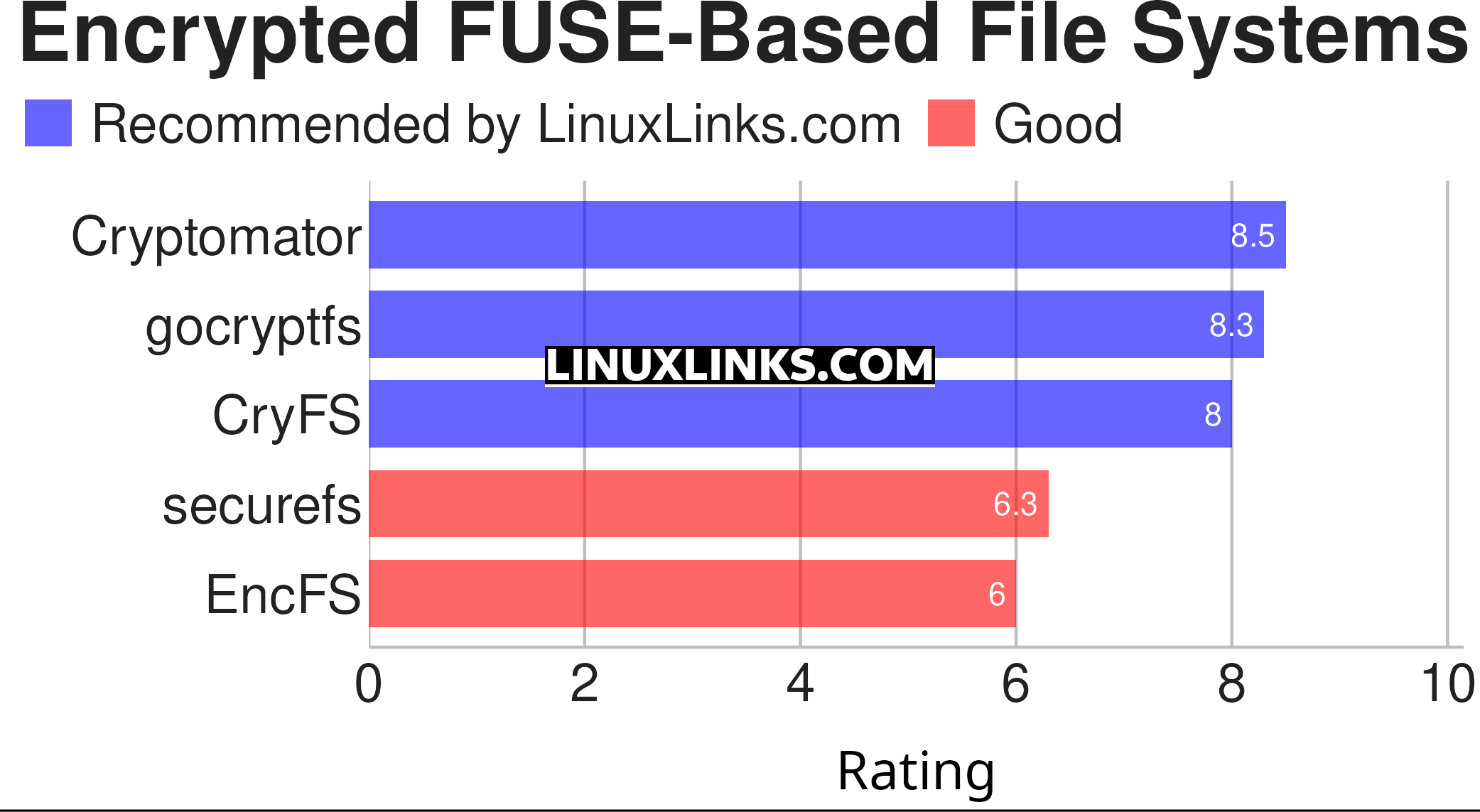
Let’s explore the 5 encrypted FUSE-based file systems. For each program we have compiled its own portal page, a full description with an in-depth analysis of its features, together with links to relevant resources.
| Encrypted FUSE-based file systems | |
|---|---|
| Cryptomator | Multi-platform transparent client-side encryption of files in the cloud |
| gocryptfs | Encrypted overlay filesystem written in Go |
| CryFS | Cryptographic filesystem for the cloud |
| securefs | Authenticated and probabilistic encryption with efficient cloud synchronization |
| EncFS | Encrypted filesystem in user-space |
This article has been revamped in line with our recent announcement.
 Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category. Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category.This directory is part of our ongoing series of informative articles for Linux enthusiasts. It features hundreds of detailed reviews, along with open source alternatives to proprietary solutions from major corporations such as Google, Microsoft, Apple, Adobe, IBM, Cisco, Oracle, and Autodesk. You’ll also find interesting projects to try, hardware coverage, free programming books and tutorials, and much more. Know a useful open source Linux program that we haven’t covered yet? Let us know by completing this form. |


You don’t want to depend on the cloud. The first 4 are all cloud based, that’s useless. You cannot trust a 3rd party to keep your data around. Constantly corporations have betrayed their users repeatedly. They cannot be trusted.
Fine to have them as a BACKUP, but that’s it. You cannot trust these companies that invade your data, delete your data, change your data.
People are foolish to trust 3rd party data at this point. They’ve stolen data, repeatedly betrayed users, deleted data without notification. They ruined Parler, destroying all their code simply because they depended on AWS for data storage.
Cloud based ANYTHING is stupid. It’s aggravating people keep pushing this crap. We got rid of the need of mainframe computing 35 years ago. Software as a service, storage as a service, is the height of naivite and and ignorance at this point. You can’t trust these corporations, they won’t even respect the 1st amendment.
I couldn’t disagree with your unqualified opinion more.
In any event, gocryptfs (one of the first four) does not require using the cloud, the encrypted files can be stored in any folder on your hard disk, or a USB stick. sucurefs and EncFS don’t need the cloud.
Only 2 of the 5 program are even targeted at the cloud.
The cloud is essential these days. Maybe not for you, but please don’t tell others what they should be using. Cloud backups are essential for most businesses these days.