Last Updated on May 28, 2022
Checksum generation and checking
A checksum is the result of running a checksum algorithm, called a cryptographic hash function, on an item of data, typically a single file. A hash function is an algorithm that transforms (hashes) an arbitrary set of data elements, such as a text file, into a single fixed length value (the hash).
Comparing the checksum that you generate from your version of the file, with the one provided by the source of the file, helps ensure that your copy of the file is genuine and error free. By themselves, checksums are often used to verify data integrity but are not relied upon to verify data authenticity.
You can create a checksum from File | Create Checksum.
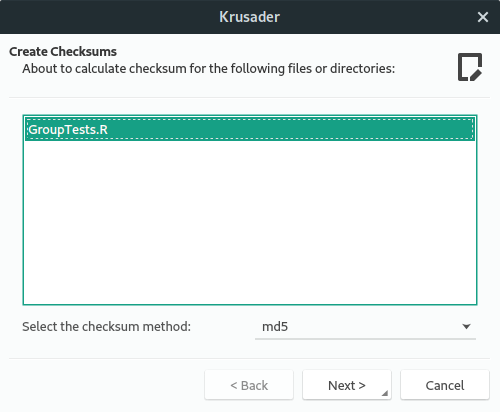
There’s the option to choose the checksum method from a dropdown list. The supported checksum methods are:
- md5 – a widely used hash function producing a 128-bit hash value.
- sha1 – Secure Hash Algorithm 1. This cryptographic hash function is not considered secure.
- sha224 – part of SHA-2 set of cryptographic hash functions. SHA224 produces a 224-bit (28-byte) hash value, typically rendered as a hexadecimal number, 56 digits long.
- sha256 – produces a 256-bit (32-byte) hash value, typically rendered as a hexadecimal number, 64 digits long.
- sha384 – produces a 384-bit (48-byte) hash value, typically rendered as a hexadecimal number, 96 digits long.
- sha512 – produces a 512-bit (64-byte) hash value, typically rendered as a hexadecimal number, 128 digits long.
Krusader checks if you have a tool that supports the type of checksum you need (from your specified checksum file) and displays the files that failed the checksum (if any).
Next page: Page 7 – Custom commands
Pages in this article:
Page 1 – Introduction / Installation
Page 2 – In Operation
Page 3 – KruSearcher
Page 4 – Synchronise Folders
Page 5 – Disk Usage
Page 6 – Checksum generation and checking
Page 7 – Custom commands
Page 8 – MountMan
Page 9 – Configuration
Page 10 – Summary


I have used Krusader in the past. The only reason that I have it installed now is because of the removal of root functions from Dolphin! I always have a separate data partition on my computers. When doing a fresh install, or a re-install, I create the data partition, but is is created as being owned by root, not my user. In the past, Dolphin had the ability to allow me to change the ownership of a directory or partition. However, the author of Dolphin made the stupid mistake of removing that functionality. Now I run Krusader as root to change properties when I need to.
GUI software should *not* be run as root. It’s simply not secure. Even if you are happy to run that security risk, it’s only right and proper that software developers make the right decisions for the majority.
Configuration Page 9 should be with Page 1 or Page 2 as this what opens after install
*should* it?
Several years have passed since that article was written, situation is better, although (for example, for the keditbookmarks case) we still can see on (for example) packages.ubuntu.com/lunar/krusader some suggested and recommended packages that Krusader may need to use.