Last Updated on January 5, 2026
Digital forensics is a specialist art. It allows investigations to be undertaken without modifying the media. Being able to preserve and analyze data in a safe and non-destructive way is crucial when using digital evidence as part of an investigation, and even more so when a legal audit trail needs to be maintained. Digital forensics can be used in a wide range of investigations such as computer intrusion, unauthorised use of computers including the violation of an organisation’s internet-usage policy, gathering intelligence from documents and emails, as well as the protection of corporate assets.
This roundup focuses on memory tools that help with forensics. Only free and open source software is eligible for inclusion here.
Here’s our verdict captured in a legendary LinuxLinks-style ratings chart.
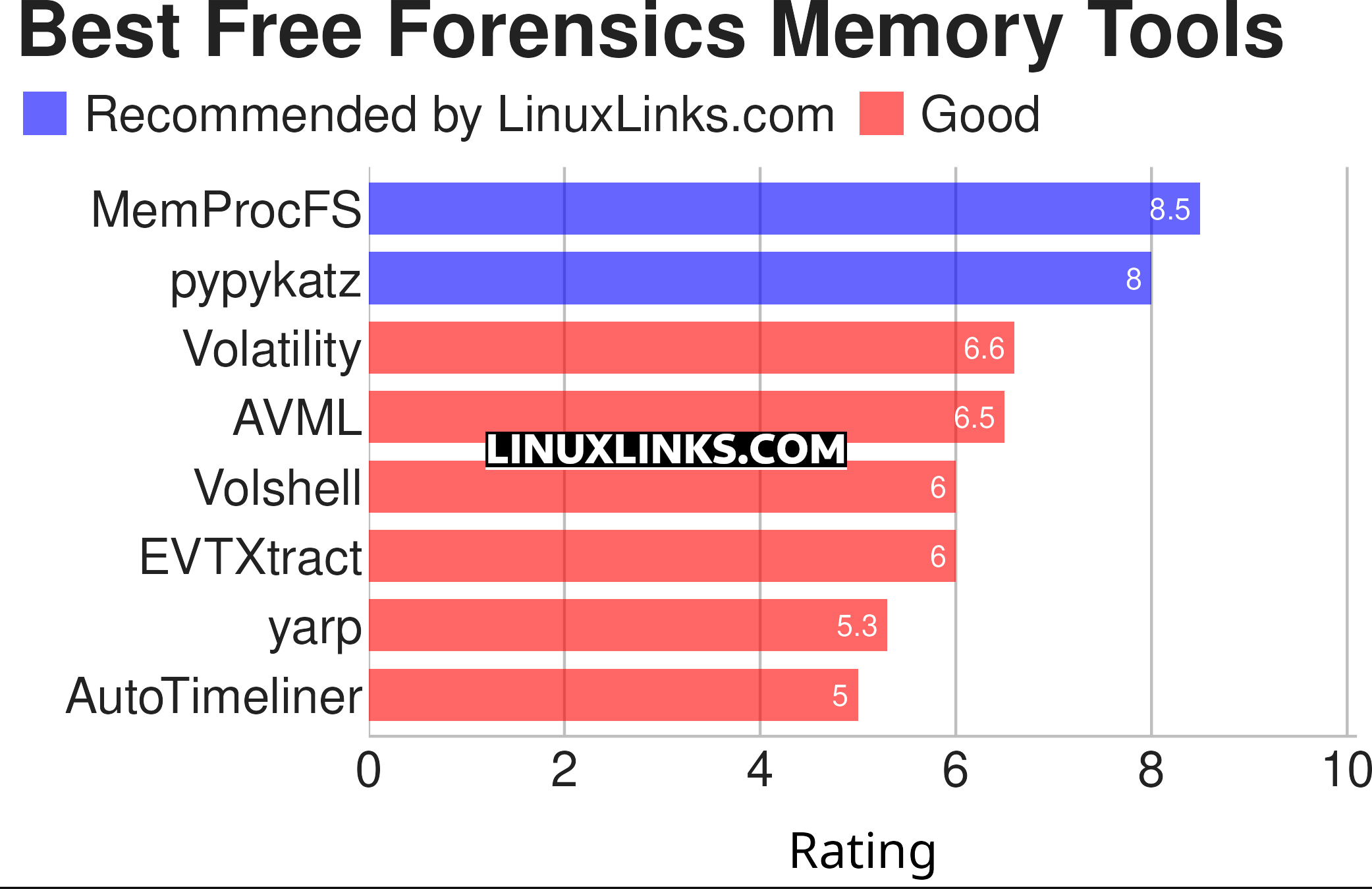
Click the links to learn more about each tool.
| Forensics Memory Tools | |
|---|---|
| MemProcFS | View physical memory as files in a virtual file system |
| pypykatz | Python implementation of Mimikatz |
| Volatility | Advanced memory forensics framework |
| AVML | Acquire Volatile Memory for Linux |
| Volshell | CLI tool for working with memory |
| EVTXtract | Recovers and reconstructs fragments of EVTX log files |
| yarp | Yet Another Registry Parser |
| AutoTimeliner | Extract forensic timeline from volatile memory dump |
 Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category. Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category.This directory is part of our ongoing series of informative articles for Linux enthusiasts. It features hundreds of detailed reviews, along with open source alternatives to proprietary solutions from major corporations such as Google, Microsoft, Apple, Adobe, IBM, Cisco, Oracle, and Autodesk. You’ll also find interesting projects to try, hardware coverage, free programming books and tutorials, and much more. Know a useful open source Linux program that we haven’t covered yet? Let us know by completing this form. |

