Security is paramount. Security involves defence in depth. Approaching security one step at a time, with consistency and rigour, you can mitigate threats, and keep intruders at bay.
Intruders use a variety of different techniques in an attempt to compromise a system. For example, systems can be attacked by denial of service, cracking, intrusion, snooping (intercepting the data of another user), or viruses/worms/Trojan horses. To have a secure box, a system therefore needs a variety of defences.
Vulnerability scanning is an essential activity for enterprise security.
Any competent enterprise will have a backbone of security measures including, but not limited to, a firewall, vulnerability scanner, asset-mapping, as well as a dedicated team that performs regular pentesting, an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system.
Recognizing, categorizing and characterizing security holes (known as vulnerabilities) among the network infrastructure, computers, hardware system, and software, etc. is known as Vulnerability Analysis.
Vulnerability scanners, in particular, are critical for ensuring that any threats that may have made it past the firewall are picked up before they can infect and undermine entire networks.
The chart captures our recommendations.
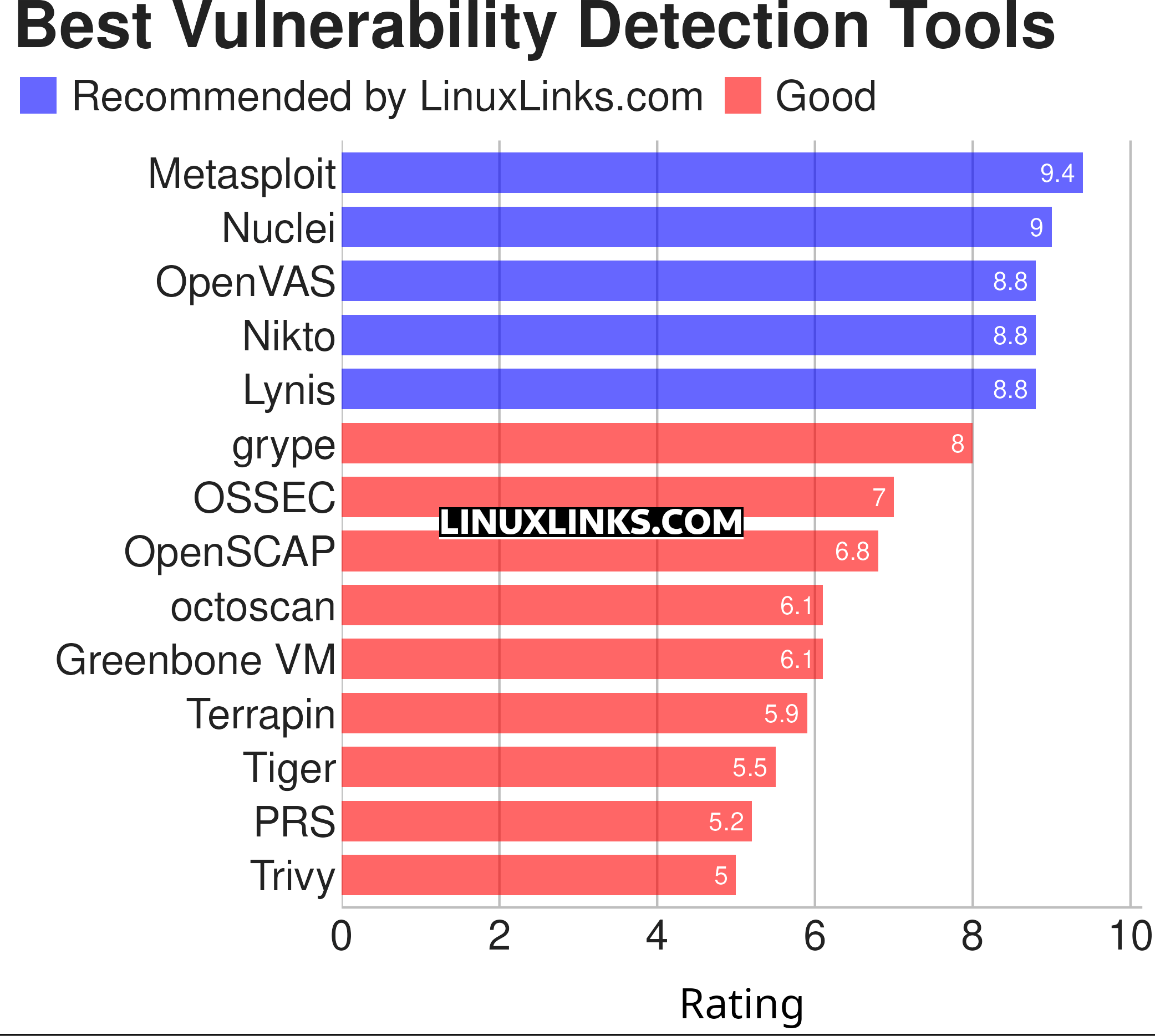
Let’s explore the 14 tools. For each application we have compiled its own portal page, a full description with an in-depth analysis of its features, together with links to relevant resources.
| Vulnerability Detection Tools | |
|---|---|
| Metasploit | Penetration testing framework |
| Nuclei | Fast and customisable vulnerability scanner |
| OpenVAS | Full-featured vulnerability scanner |
| Nikto | Web server scanner |
| Lynis | Auditing, system hardening, compliance testing |
| grype | Vulnerability scanner for container images and filesystems |
| OSSEC | Centralized architecture for monitoring and managing multiple systems |
| OpenSCAP | NIST Certified SCAP 1.2 toolkit |
| octoscan | Static vulnerability scanner for GitHub action workflows |
| Greenbone | Central management service between security scanners and the user clients. |
| Terrapin | Terrapin Vulnerability Scanner for the Terrapin attack |
| Tiger | Security audit and intrusion detection too |
| PRS | Web security scanner |
| Trivy | Terrapin Vulnerability Scanner for the Terrapin attack |
This article has been updated to reflect the changes outlined in our recent announcement.
 Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category. Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category.This directory is part of our ongoing series of informative articles for Linux enthusiasts. It features hundreds of detailed reviews, along with open source alternatives to proprietary solutions from major corporations such as Google, Microsoft, Apple, Adobe, IBM, Cisco, Oracle, and Autodesk. You’ll also find interesting projects to try, hardware coverage, free programming books and tutorials, and much more. Know a useful open source Linux program that we haven’t covered yet? Let us know by completing this form. |

