There are two common methods of performing system fingerprinting: active and passive scanning.
The more common active methods use responses sent to TCP or ICMP packets. The TCP fingerprinting process involves setting flags in the header that different operating systems and versions respond to differently. Usually several different TCP packets are sent and the responses are compared to known baselines (or fingerprints) to determine the remote OS.
For stealthy detection, there’s the option of passive fingerprinting. Unlike the active method, this style of fingerprinting does not send any packets, but relies on sniffing techniques to analyze the information sent in normal network traffic. This way there are no deliberate changes or actions against the network.
Passive OS Fingerprinting is a more stealth, but far slower process and usually less accurate than a targeted active fingerprinting session.
This type of software is often used for a variety of activities including, but not limited to, reconnaissance during penetration tests, routine network monitoring, detection of unauthorized network interconnects in corporate environments, providing signals for abuse-prevention tools, and miscellaneous forensics.
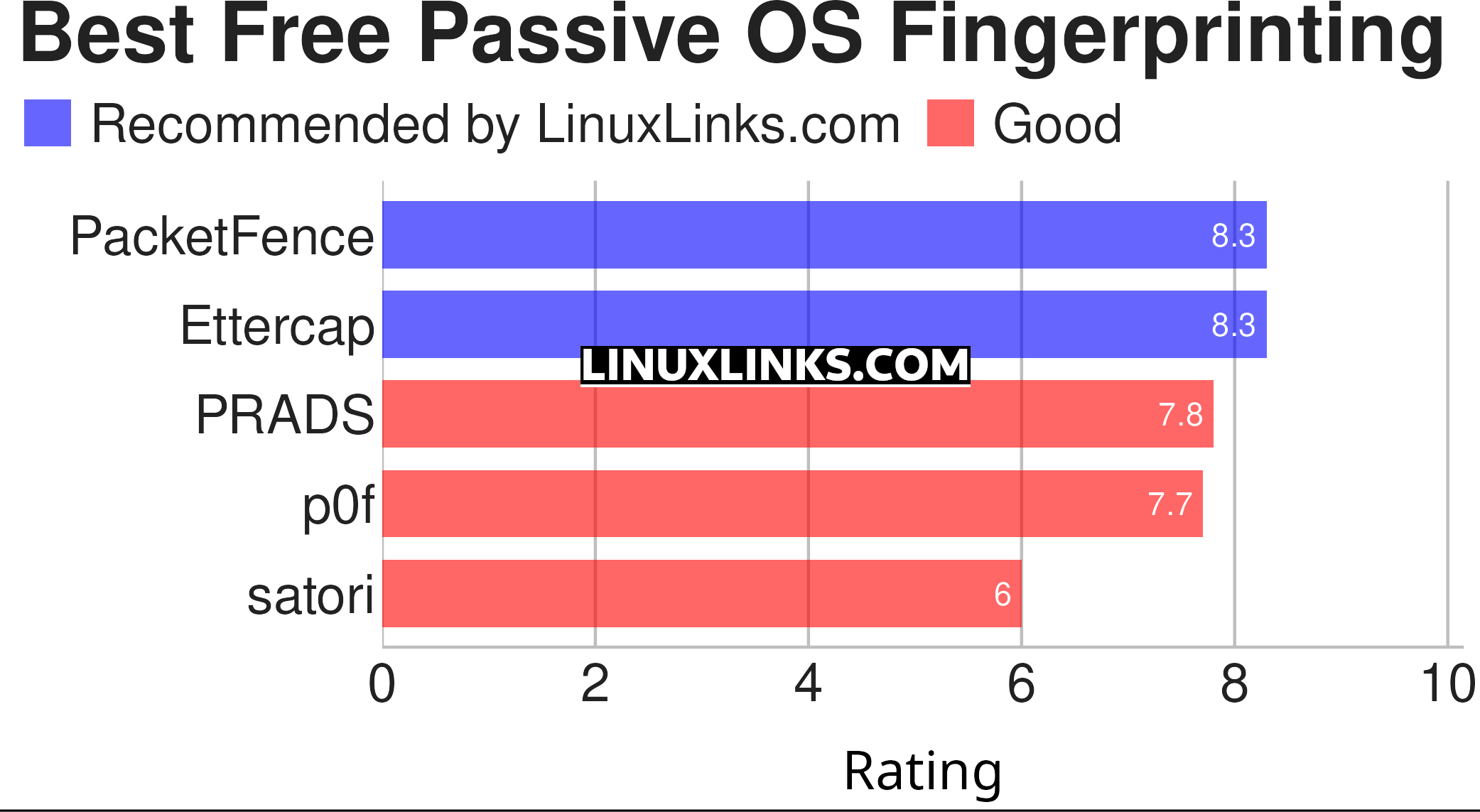
Here’s our verdict captured in a legendary LinuxLinks chart. Only free and open source software is included.
Let’s explore the 5 fingerprinting tools at hand. For each title we have compiled its own portal page, a full description with an in-depth analysis of its features, a screenshot of the software in action, together with links to relevant resources.
| Passive OS Fingerprinting | |
|---|---|
| PacketFence | Network access control solution with passive DHCP fingerprinting |
| Ettercap | Comprehensive suite for man in the middle attacks |
| PRADS | Passive Real-time Asset Detection System |
| p0f | Array of passive traffic fingerprinting mechanisms that are highly scalable |
| satori | Python rewrite of passive OS fingerprinting tool |
This article has been revamped in line with our recent announcement.
 Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category. Explore our comprehensive directory of recommended free and open source software. Our carefully curated collection spans every major software category.This directory is part of our ongoing series of informative articles for Linux enthusiasts. It features hundreds of detailed reviews, along with open source alternatives to proprietary solutions from major corporations such as Google, Microsoft, Apple, Adobe, IBM, Cisco, Oracle, and Autodesk. You’ll also find interesting projects to try, hardware coverage, free programming books and tutorials, and much more. Know a useful open source Linux program that we haven’t covered yet? Let us know by completing this form. |


As the author of Satori I love to see that it is on the list, though I’m sad to see I’m beat out by a number of programs that haven’t been updated in years!
But is their software better than yours? There’s lots of great Linux software that’s not under active development. For many types of software the last update is not necessarily a big factor.
It depends on what you want to fingerprint. Satori handles tons of protocols, where most of the others primarily only do TCP fingerprinting. Pros/cons of to all of them for sure though.
The important thing is that we have choices.